ExeonTrace Xlog
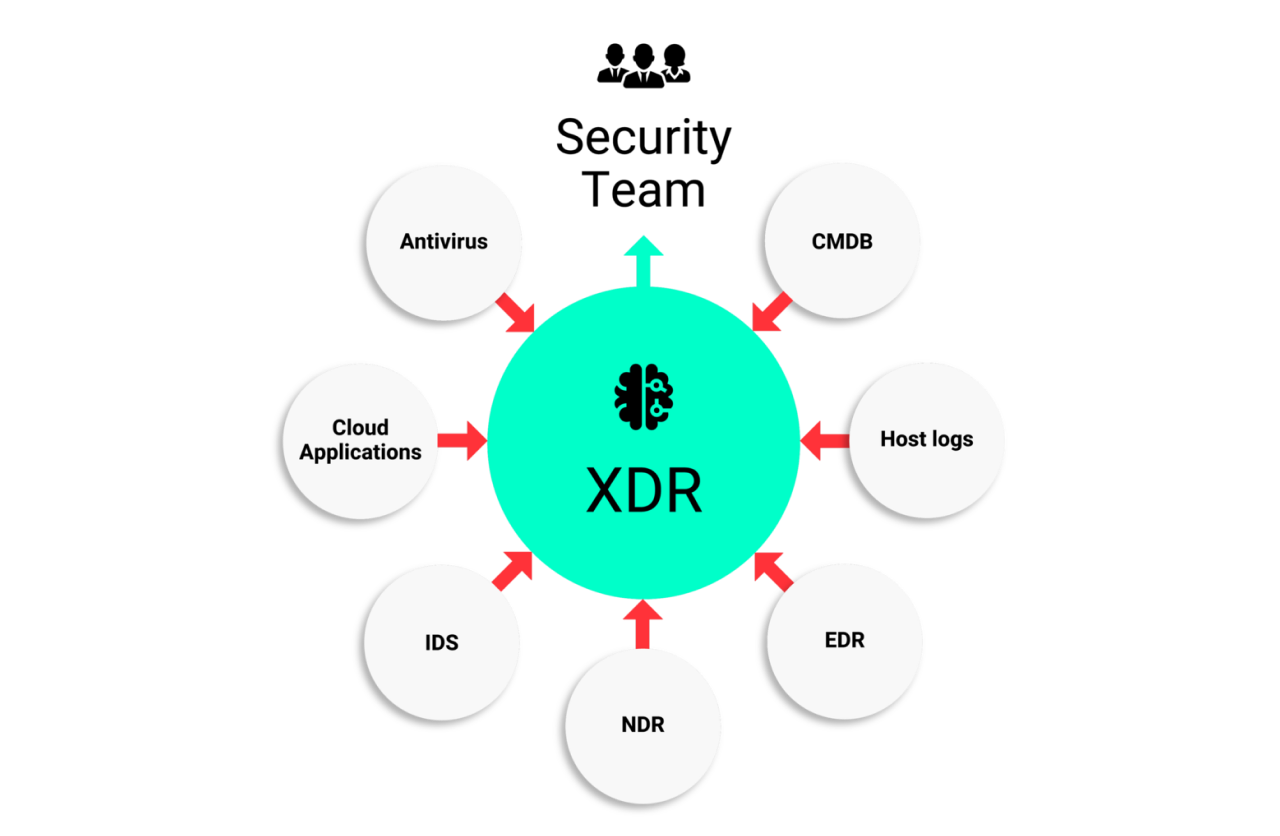
Extending NDR to XDR: Cross-data threat detection and a unified view of networks, endpoints and applications with the Xlog analytics kit for your custom log data.
Turn NDR into XDR
Extend your cyber security capabilities and processes with ExeonTrace Xlog
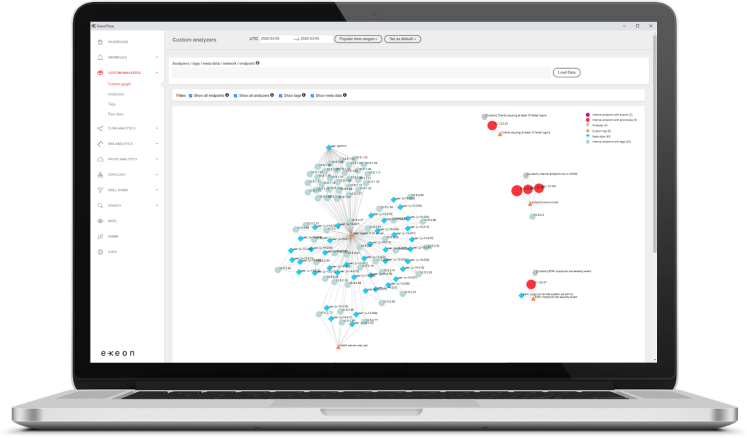
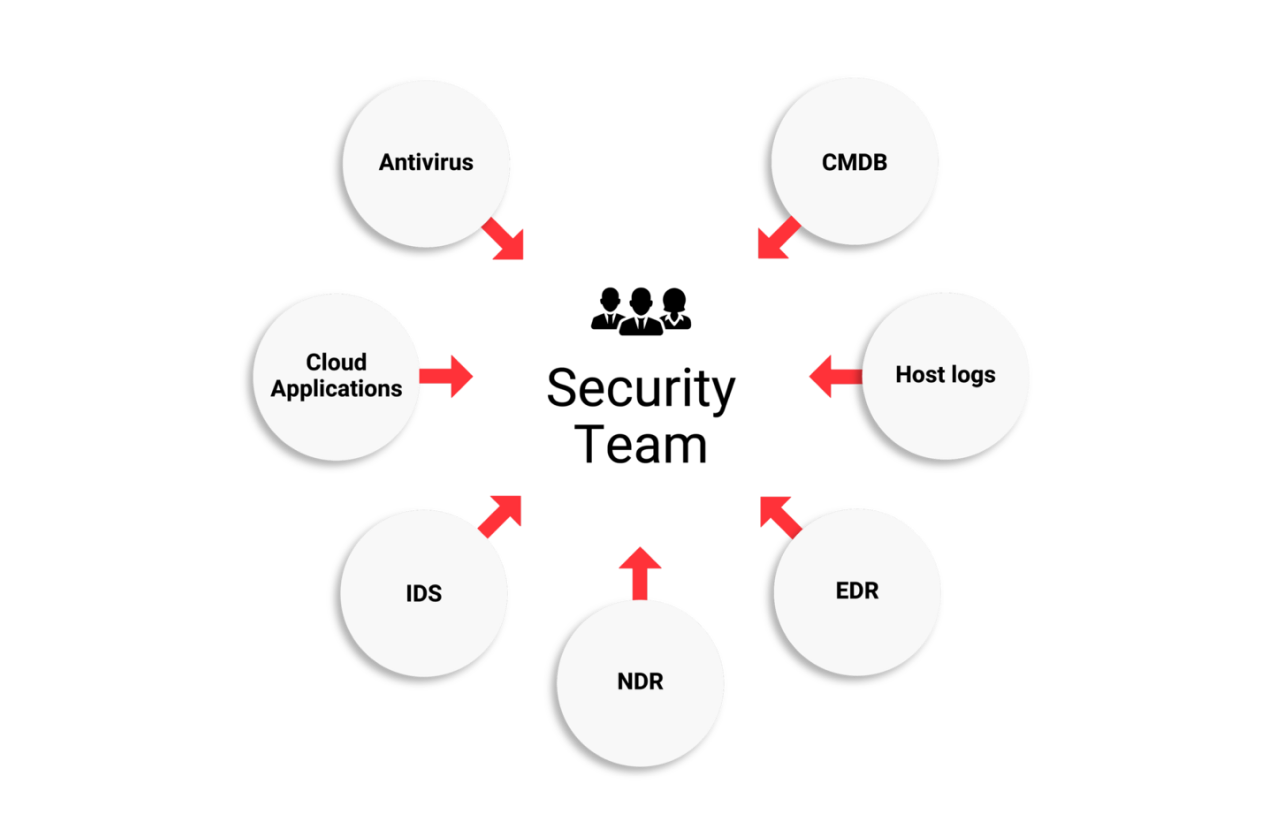
Are you struggling to apply meaningful security analytics across your various data sources? Even with a SIEM solution in place, many SOC teams struggle to implement cross-data anomaly detection and threat hunting. The new Xlog module extends our ExeonTrace Network Detection & Response (NDR) platform beyond the network - to a unified IT infrastructure visibility and protection solution. It gives you unified monitoring, detection and response capabilities across your distributed networks, endpoints and applications - all in one place.
Extend Your Analytics
By integrating log data from endpoints, cloud- and host-based applications, correlating it with network security data, and automatically analyzing it with AI and prebuilt detection scenarios, the Xlog module drastically improves your cyber protection. Xlog turns the ExeonTrace NDR platform into a powerful Extended Detection & Response (XDR) solution. Your entire IT landscape is now at your fingertips, in one central interface. View and monitor all your assets, detect threats across systems, and respond faster than ever before. A powerful alternative to your SIEM.
Reduce the workload
Reduce the workload of your security team by providing automated analysis, detection, and threat assessment across your IT landscape, all in one place. Complete overview, quick detection, and fast response, all while minimizing false alarms and providing important investigation context.
Xlog, the analytics toolbox for your custom log data
Artificial Intelligence
AI for automated anomaly detection across various log data sources (network, cloud, application and host log data).
Enhanced Visibility
Unified visibility thanks to high-level graph visualizations and consolidated views.
Fast detection with minimum false alarms
Combining host- and network-based detection results to faster identify threats and minimize false alarms.
More storage and faster data retrieval
Graph database reducing raw logs to security-relevant information to save storage space and speed up data retrieval.
Unique algorithms
Out-of-the-box and custom made detection algorithms for a quick start.
Xlog Module: Cross-data threat detection
For additional security relevant log data