ExeonTrace vs. Competition
The Most Advanced NDR Solution for Corporate Networks
To deal with expanding attack surfaces of increasingly complex IT environments, network detection and response (NDR) solutions have undoubtedly become a crucial part of a robust cyber architecture. However, there are significant differences in NDR solution’s detection technologies and analysis capabilities.
While most traditional NDR providers rely on deep packet inspection, more future-proof approaches such as ExeonTrace use metadata analysis.
Sensor/Switch
(Providing data for analysis)
Sensor/Switch
(Not providing data for analysis)
Data flow
(Visible)
Data flow
(Non-visible)
Device
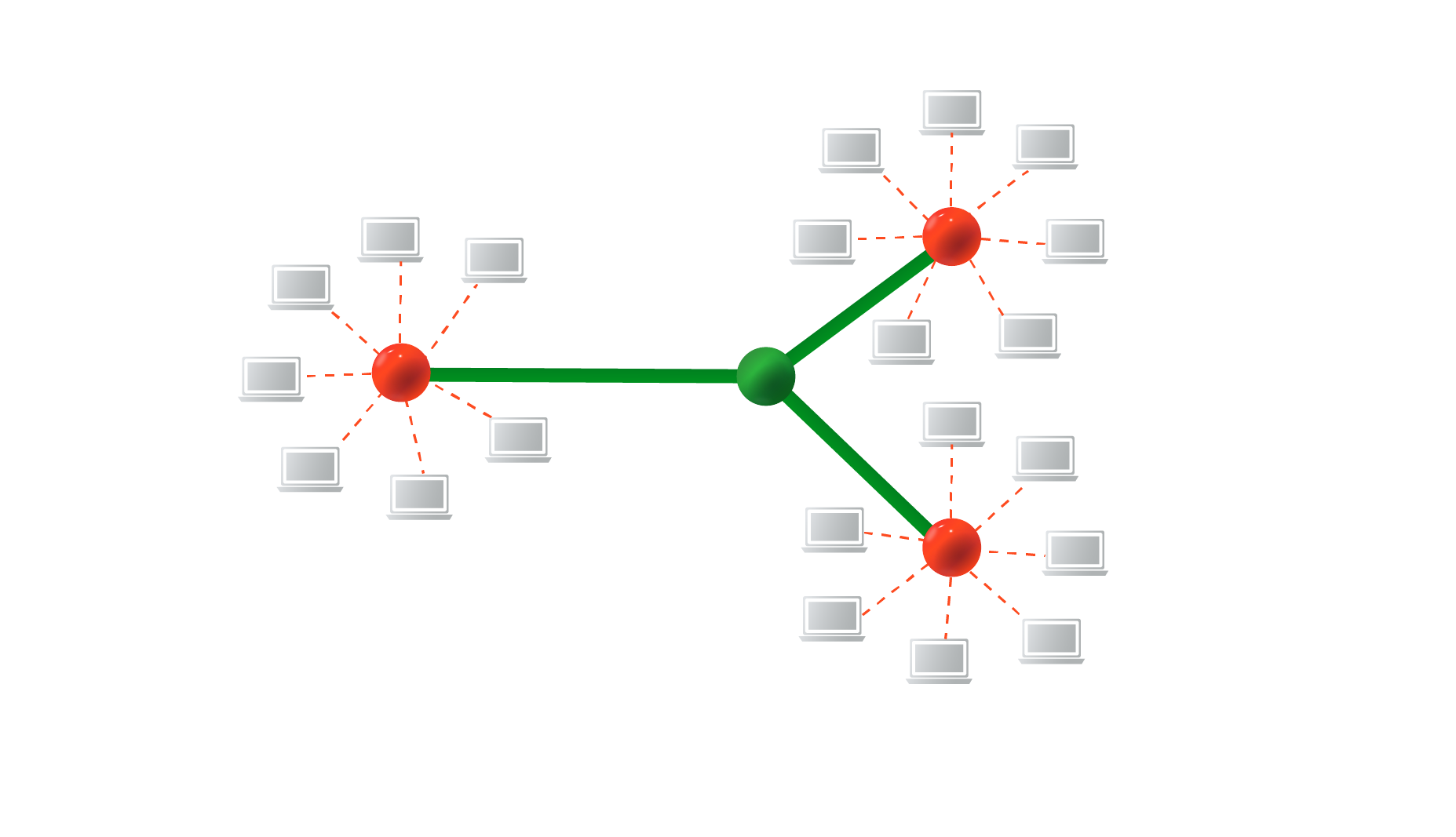
What they see:
Only the traffic flowing via mirrored switches.
What we see:
All network communications passing through any physical and virtualised networks.
Deep Packet Inspection
Deep Packet Inspection (DPI) relies on Traffic Mirroring and is a type of network filtering used to inspect the entire payload of packets flowing across specific connections or core switches. DPI’s analysis capabilities are limited to the network traffic transmitted on the monitored core switches and require large amounts of computing power, making it unsuitable for high-bandwidth networks. In addition, the rapid adoption of encryption (encrypted legacy protocols, SSL certificates etc.) hinders DPI to inspect the payloads, even though the customers provide terabits of mirrored packed payloads.
Metadata Analysis
Metadata Analysis (MA) has been developed to overcome the limitations of Deep Packet Inspection. Instead of being limited to only inspecting the traffic flowing across core switches, MA relies on log data (NetFlow/sFlow/syslog etc.) from multiple network sources (Switches, Cloud logs, Firewall etc.). For every packet passing through the network (via virtual and core switches), the source/destination IP address, session length, protocol (TCP, UDP) and types of services used are recorded and analysed. This provides security teams with real-time intelligence of all network traffic. NDR solutions relying on MA do not require any hardware sensors, can deal with ever-increasing network traffic and are completely unaffected by encryption. This approach supplemented by system- and application-logs (such as DC logs) allows for more insights than DPI.
Capabilities
Traditional NDR solutions
Traditional NDR solutions
Analysis of light-weight log data – no traffic mirroring, no additional hardware
Metadata analysis, unaffected by encryption
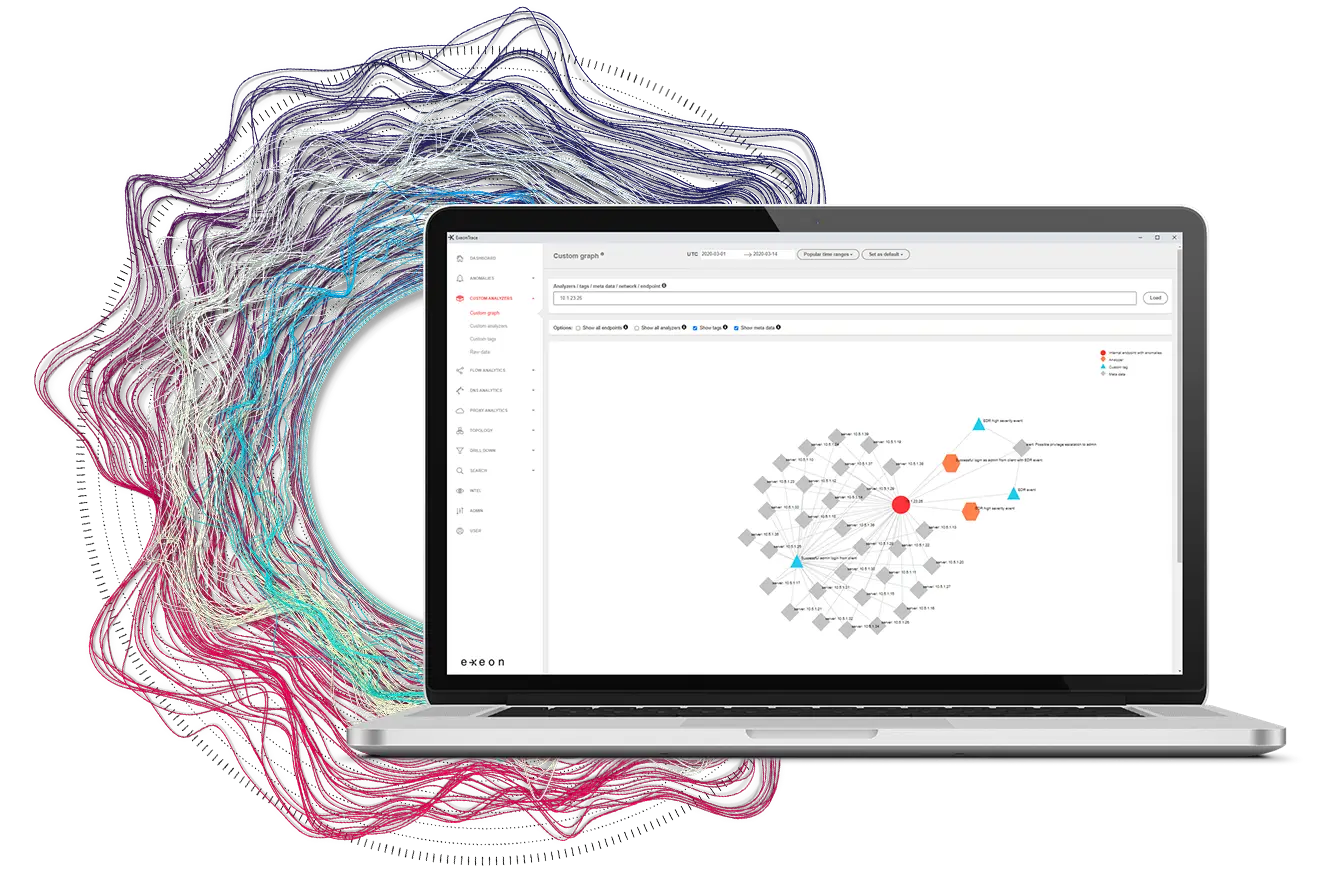
Holistic visualisation of IT network
Holistic visualisation of IT network
Powerful Machine Learning algorithms
Powerful Machine Learning algorithms
Why our customers continue to choose us over traditional NDR providers:
Supervised & Unsupervised ML algorithms
ExeonTrace is equipped with supervised and unsupervised machine learning algorithms designed to analyse billions of network interactions and detect sophisticated cyberattacks, such as APT, ransomware and lateral movement.
Metadata analysis unaffected by encryption and increasing bandwidths
Unlike NDR providers relying on deep packet inspection, ExeonTrace is entirely unaffected by traffic encryption and increasing bandwidths since its algorithms were specifically built for the analysis of metadata.
Holistic visibility into entire IT/OT network
By relying on Metadata Analysis, ExeonTrace provides complete visibility into all network communications passing through any physical, virtualised or cloud networks.
Analysis of light-weight log data
Analysis of light-weight log data (NetFlow/sFlow/syslog) instead of data-heavy traffic mirroring. Metadata can be exported from existing network sources (switches, firewalls etc.) without hardware sensors.
Efficient log data storage
By reducing input log data by a factor of 100, our specialised algorithms support light-weight storage of historical data for later inspection, making ExeonTrace optimal for high-bandwidth networks.

Patrick Käppeli
Network & Security Engineer, Solothuner Spitäler
Exeon is our cybersecurity alarm system, alerting us to any network anomalities. What also really convinced us is the intuitive interface of the platform – it has become a tool to reliably monitor and secure our data and network.

Christian Keller
CISO, SWISS Airlines
As the Swiss national airline, we are driven by a passion for exceptional performance, in the spirit of our guiding principles. A stable and secure IT is the most important basis for an excellent customer service. For the security of SWISS IT we use Exeon as a central cybersecurity tool, fully managed by our long-term partner Reist Telecom AG. A perfect combination and solution to monitor our network and quickly detect any kind of anomalies.

Peter Hagen
CIO, Planzer
I’m highly impressed by the technical abilities of this Network Detection & Response solution. I can definitely sleep better knowing that we have ExeonTrace in our network.