CISO Challenge #3
Writing and maintaining SIEM use cases for network log data is cumbersome
Many companies that don’t have a dedicated NDR solution in place yet, aim to analyse network logs with their SIEM. However, writing reliable use cases for network log data with a SIEM is difficult for several reasons. First, NetFlow/IPFIX, which is the dominant industry standard for network traffic logging, logs each connection direction separately. SIEMs typically lack functions to create a holistic view of these individual log entries. Secondly, SIEMs lack specific machine learning models for network traffic. Third, there can easily be billions of data points per day, causing major scalability issues. And lastly, due to the massive amount of data points, the accuracy of use cases must be very high to avoid too many false positives.
Exeon’s approach
- ExeonTrace’s algorithms, which are based on research from ETH Zurich, reconstruct a consistent representation from billions of network log data points. This allows ExeonTrace to run advanced detection models on billions of data points on a single commodity VM with high accuracy
- ExeonTrace comes with use cases that combine supervised ML, unsupervised ML, expert knowledge, and traditional IOCs
- These use cases are managed by Exeon
Benefits for CISOs and security teams
- Scalable, high-quality detection for network traffic logs, with very few false positives
- Use cases are updated by Exeon
- No need to manually write and maintain use cases
Unique benefits of ExeonTrace

Comprehensive visibility
Visibility into your entire IT/OT network and all its interfaces to identify vulnerabilities (exposed services, shadow IT etc.) and malicious attack patterns in real-time.

Not affected by encryption
Algorithms are unaffected by encrypted payloads since they are built to detect attack patterns based on metadata and not deep packet inspection.
Light-weight log data
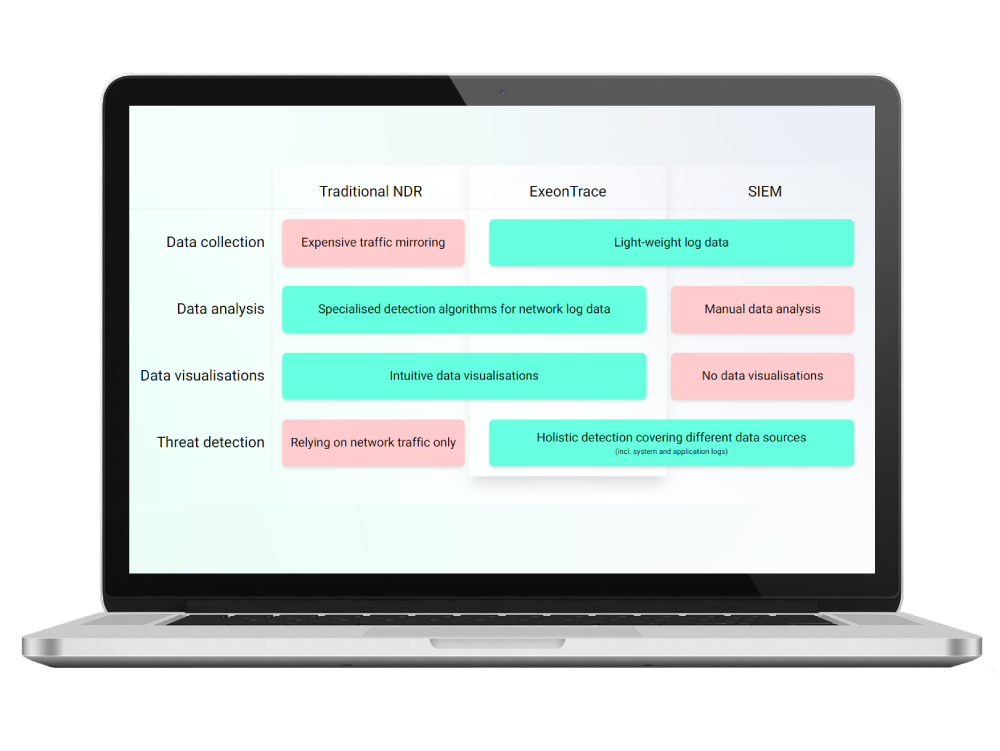
Analysis of light-weight network log data instead of data-heavy traffic mirroring. Metadata can be exported from existing network sources (switches, firewalls etc.) without hardware sensors.

Developed in Switzerland
As an established Swiss NDR solution, based on a decade of research at ETH Zürich, we maintain a high level of innovation and privacy, which is incorporated in our ExeonTrace platform.