CISO Challenge #2
Network traffic encryption makes my tools, which rely on deep packet inspection, become blind
The increasingly encrypted network traffic poses a significant challenge for security tools that rely on deep packet inspection. And the trend is clear – the proportion of encrypted traffic will only rise in the future.
Exeon’s approach
- ExeonTrace works with algorithms that analyse meta data (NetFlow)
- These algorithms, which are based on Exeon’s research at ETH Zurich – one of Europe’s leading high-tech universities – are unaffected by traffic encryption
- The log data come from firewalls, virtual/physical switches (NetFlow, IPFIX), DNS, secure web gateways, clouds (Azure, Google, AWS)
Benefits for CISOs and security teams
- Existing infrastructure is leveraged, no need for additional appliances
- High alert accuracy (our meta data-based algorithms regularly outperform packet inspection-based competitors)
- No blind spots in the network
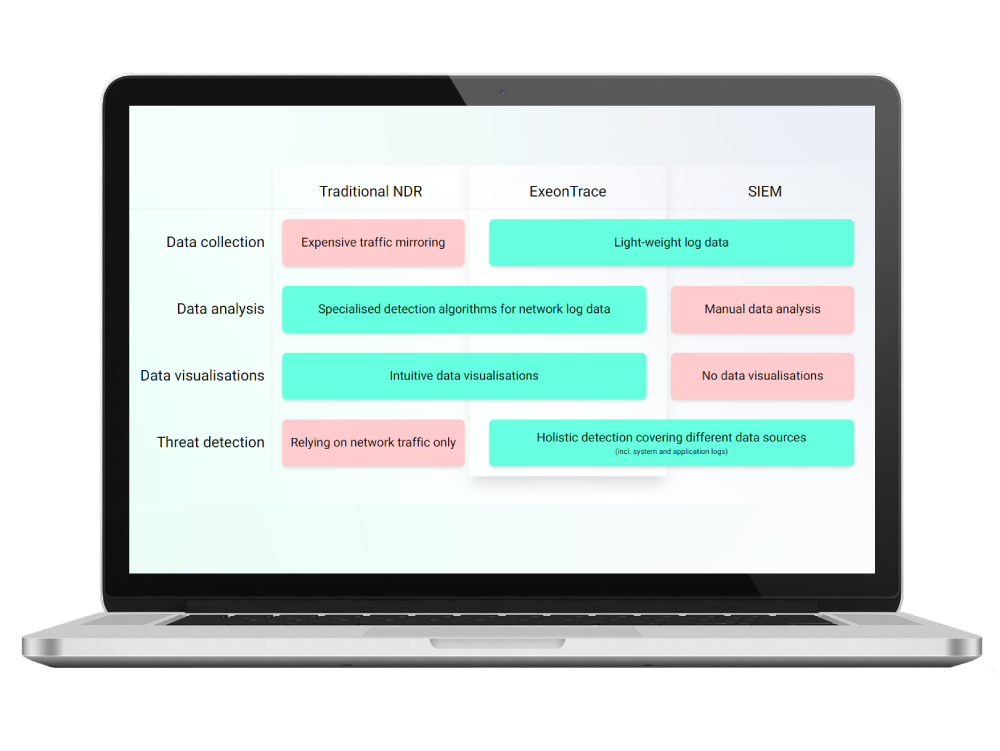
Unique benefits of ExeonTrace

Comprehensive visibility
Visibility into your entire IT/OT network and all its interfaces to identify vulnerabilities (exposed services, shadow IT etc.) and malicious attack patterns in real-time.

Not affected by encryption
Algorithms are unaffected by encrypted payloads since they are built to detect attack patterns based on metadata and not deep packet inspection.
Light-weight log data
Analysis of light-weight network log data instead of data-heavy traffic mirroring. Metadata can be exported from existing network sources (switches, firewalls etc.) without hardware sensors.

Developed in Switzerland
As an established Swiss NDR solution, based on a decade of research at ETH Zürich, we maintain a high level of innovation and privacy, which is incorporated in our ExeonTrace platform.